Nvidia's DeepSeek challenge led to $600bn market value loss, with CEO Jensen Huang losing $21bn. Tech stocks plummet as AI world faces potential turmoil.
Part 2 explores Raspberry Pi Pico PIO quirks in programming a musical instrument. Wat 5 reveals issues with constants, urging creative workarounds.
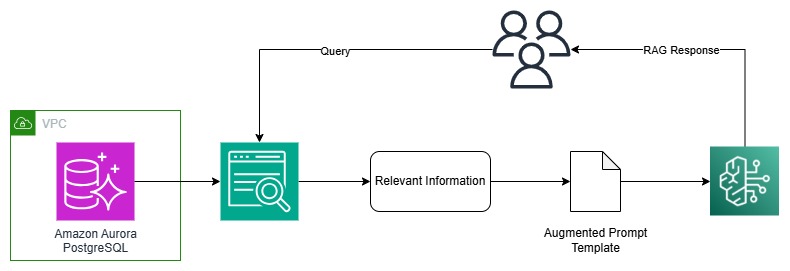
Generative AI and large language models are transforming organizations by enhancing customer experience through data conversion. Amazon Aurora enables easy data indexing for Amazon Kendra to implement Retrieval Augmented Generation (RAG) for accurate responses.
Chinese startup challenges US AI dominance. Stargate initiative by Trump, Altman, Son, and Ellison. Meta to invest $65bn in data centers.
DeepSeek's app faces cyber-attack after becoming top free app in US, prompting temporary registration limit. Despite the setback, existing users can still access the AI assistant app as company investigates the large-scale malicious attack.
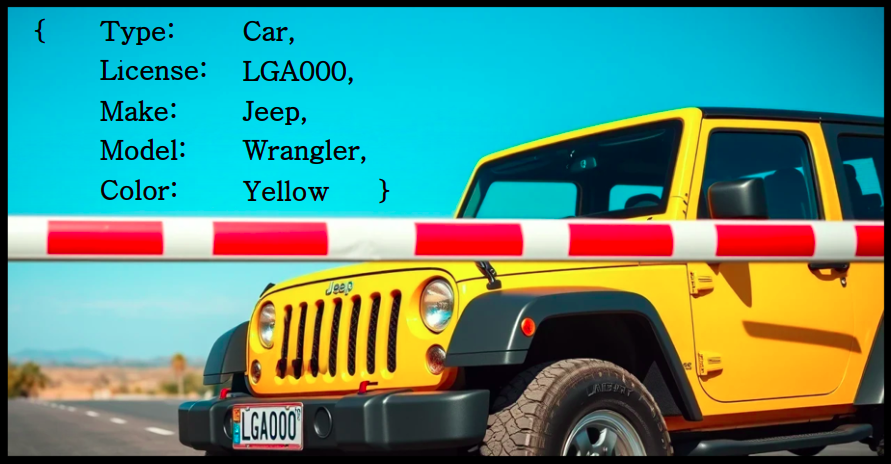
Build a vehicle documentation system using OpenAI's GPT-4, LangChain, and Pydantic for structured data extraction from images. Simplify complex workflows with LangChain and ensure output consistency with Pydantic for easy downstream use.
Investors wary as China's DeepSeek AI chatbot disrupts US tech stocks with cyber-attack. Doubts arise over sustainability of US AI boom due to emergence of cheaper Chinese alternative.
Luca Carlone at MIT's SPARK Lab aims to enhance robots' perception to enable seamless human interaction in various environments. By bridging the gap between human and robot perception, Carlone's work could revolutionize how robots assist in real-world scenarios.
Chinese AI app DeepSeek outperformed OpenAI's ChatGPT, topping Apple charts, but dodged sensitive questions about China and its government. Despite its popularity, the chatbot censors answers on controversial topics.
Guide to classifying sensor data using UCI HAR dataset with TS-Fresh & scikit-learn. Learn how to extract insights from time-series data for human activity recognition.
AI could undermine democracy by replacing human labor, says Simon Steyne. David Hardiman argues revolution may come from across the class divide, not just working-class militancy.
Amazon introduces Nova Canvas and Nova Reel for image and video generation, transforming text and image inputs into custom visuals for professional and personal projects. Effective prompts are key to unlocking the full potential of these models, guiding users on how to communicate their vision effectively for optimal results.
Elton John supports Paul McCartney in defending copyright laws, urging new rules to protect artists' livelihoods from tech companies. Proposed amendments aim to extend copyright protections in the UK ahead of a crucial House of Lords vote.
Thinktank report suggests government intervention crucial for supporting businesses through automation transition. IFOW warns of increased inequality without action to assist small businesses and workers.
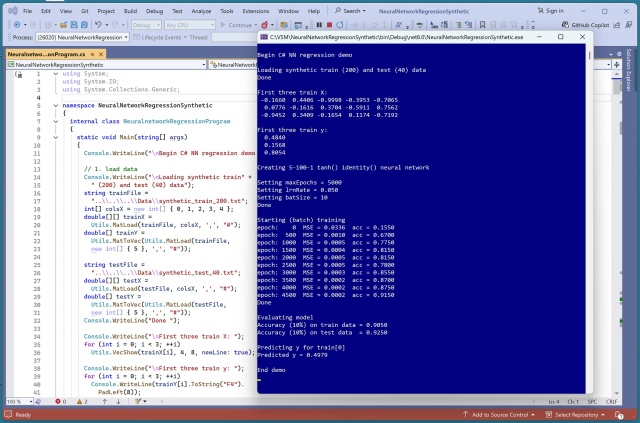
C# machine learning implementations aim to mimic scikit-learn's API design for consistency. Debate arises over passing all parameters to constructors versus just training data to methods.